Responsible Reuse of data
For business customers
Responsible – ethical data marketplace meeting all compliance and security needs d secondary use can be created with the consent of the users

Responsible Reuse of data
For business customers
Responsible – ethical data marketplace meeting all compliance and security needs

Ethical personal data market
Secondary usage of data is in the interest of all parties. The reData.me platform enables all stakeholders in a personal data market to engage in ethical data trading that is built around the consent of the data subjects (a person whom the data is about).
Data monetization
Many companies collect a lot of data that would be suitable for purposes other than their original purpose. But due to the personal nature of the data, despite the lost opportunity on both ends, it cannot be monetized. The reData.me platform creates the possibility to use data grouped into packages, which the organization offers for sale in a way that consent and authorization for the final transfer of the data always comes from the data subject.


Data purchasing
Service providers often cause unnecessary inconvenience to customers by requesting data, which is already available elsewhere. In addition, there are many opportunities where, if service providers had access to personal data, they could offer services that they might never be able to offer by relying on their own data collection. With the help of the reData.me platform, it is possible to build a service, based on compliant data retrieval, where the data is stored at other companies, and its use requires the consent of the data subject.
Three-sided transaction - four-sided interest
The reData.me platform connects the parties with the data (data holder), the parties intending to use the data (data user) and those whom the data is about (data subject). We believe that if all parties are interested in the transaction, data utilization can result in a better customer experience, new services, or new research. That is why we have developed a business model that is profitable and transparent to all parties while complying with the legal and security requirements.
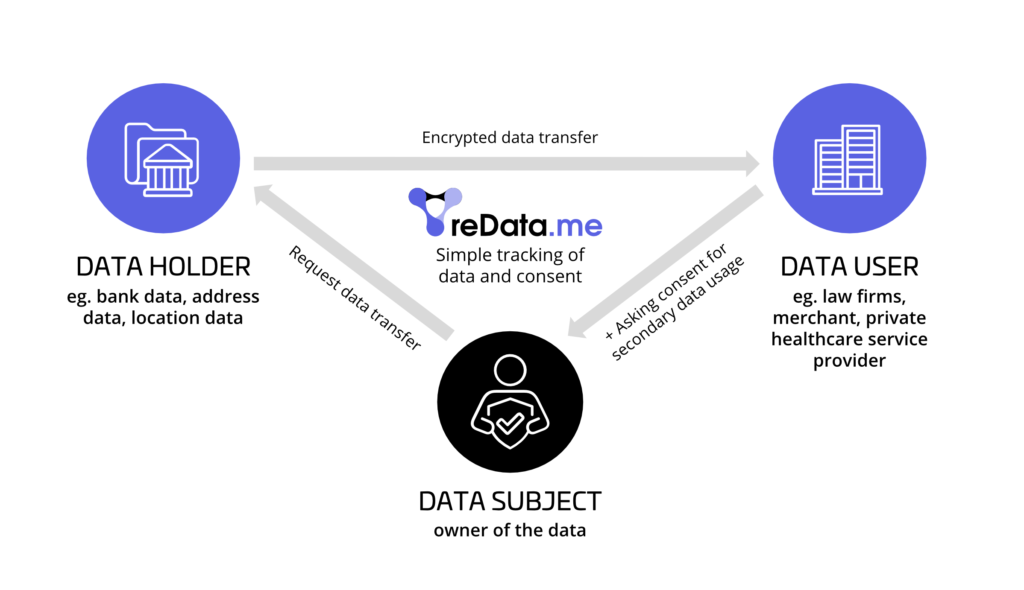
Data holder side
We allow data holders to define so-called data packages and set the price for data re-use. The description and the price of the data packages will be displayed on the reData.me data marketplace where data users can browse. If a data user launches a service based on data package, data holder receives a re-use fee, paid by data user. In this way, the accumulated data capital can indeed be converted into assets with a turnover value.

Data user side
We allow data users to browse between data packages to create data request forms containing offers for data subjects (end users) and the data they intend to request. This gives data users a clear understanding of what data they can use, for what purpose and how much the transaction will cost. Only actually received data has to be paid. This allows data users to make a precise business calculation and to start a new data-based service and re-use valuable data.

Data subject side
Data subjects are the ones who benefit the most on the reData.me platform, as they can control the re-use of their data and enjoy the added value of new services while using the system completely free of charge. Moreover, in some cases, they might receive direct compensation for the special use of their data, such as R&D purposes.
reData.me side
The reData.me platform has a transaction fee-based business model. 10% of the data re-use fees paid is spent on the operation and development of the reData.me. With this model, reData.me is also interested in having the most transactions possible on its platform. This allows to make as much money as possible for data holders and generate as much value from the data re-use as possible.
Due to the well-designed business model, joining the reData.me platform is free of charge for all parties. Only the delivered data re-use transactions have to be paid for.
Due to the well-chosen business model, integrating with the reData.me platform is free of charge, you only have to pay for the transactions that were delivered.
One integration - many connections
By connecting to the reData.me platform, your organization can join a number of organizations that want to participate in ethical data trading with one single integration. Joining is easy and free.
Technical integration
During technical integration, we install a so-called Local reData Gateway (LRG) to create a node for your organization to participate in encrypted data transfers and data re-use. We ensure the management of private and public keys, integration with databases and connection to the necessary customer authentication procedures.
Defining supply and demand of the data
On the data supply side (data holder), it is possible to define and describe data packages, which can be shared only with user consent. The details and metadata about the defined data packages is displayed in the reData.me data market.
On a data request side (data user), it is possible to define the data request form per each business case the company has, in which it can be specified which data packages your organization would request for a specific business process. Data request forms defined in this way can be easily integrated into data user’s solutions so that customers can be easily informed about new opportunities with reData.me.
Transactions
When a data user initiates a data request from the data holder on behalf of data subject, the reData.me platform collects data subject’s consent and redirects him to the holder of the selected data package, where after a successful identification the transfer of the encrypted data will be performed.
Settlement
Settlement, clearing and invoice issuance are executed between data-trading parties on monthly basis. The activity history and analytics are available real-time in the reData.me platform.

Safe, Secure and Compliant
The reData.me platform pays particular attention to ensuring that the framework it provides meets all safety and security standards. Ensuring both security and compliance is of paramount importance for us.
Security
Our system is designed not only on policy level, but also technologically to eliminate potential misuse, keep focus on our customers and act in their best interest.
No-access policy
The reData.me system is designed to protect data from any unauthorized access. The transferred data is encrypted on the data holder’s server with the data user’s public key, which can only be unlocked with the data user’s private key. Because of this, if anyone, anywhere could gain unauthorized access to a data package during the transfer, they would not see anything. For the same reason, even reData.me platform does not have access to the transferred data.
Data holder side authentication
When a user requests the transfer of data, after identifying the set of the data, the user is redirected by the reData.me to the data holder’s page, where the user has to perform a successful authentication. Therefore, the data holder can verify the request legitimacy (purpose limitation check) and who is the user (user identification) to whom it is required to disclose the data. With this technology, we can ensure that even the reData.me platform does not know who the user is. All we need to know is that it has the ability to authenticate at the data holder’s side.
Transactions logging
It is important for the reData.me platform to be able to keep a traceable record of when, by whom and for what purpose your data was used. This information is stored using an unforgeable log and SAML protocol, which allows to have a clear and verifiable status of which transactions have been performed with which legal base at any time. The similar secure logging and encryption methodology and technology are used for citizen authentication across Europe.
Legal compliance
The use, especially re- use, of data in Europe is determined by the GDPR framework. In addition, a number of European policies are now being developed that will frame the transfer and trade of data. The reData.me was designed to ensure that the parties using the platform for data trading can easily comply with current regulations and by keeping our finger on the pulse of future directives we guarantee to always stay up to date.
Purpose limitation
In the system, in order to use the data, it should be clarified exactly what purpose the requesting party (data user) will use it for and what benefit will the end-user (data subject) derive from it. When consent is given, this is read and approved by the users (data subjects), thus maximizing the expectation of purposeful, informed consent (GDPR Articles 6,7).
Data transmission on request
Data-sharing is always a sensitive operation from a legal point of view. In the reData.me system, when a data subject agrees that a data package can be used for a specific purpose, at the same time a data transfer request is made to the data holder to transfer this data package. Thus, the data holder has a clear legal basis for sharing the requested data on the grounds of the right to data portability (GDPR Article 20).
Data sharing service provider
A central element of the architectural design of the reData.me platform was that it should not be able to look into the data it conveys. Thus, reData.me cannot provide data analysis services, and it has a clear role in the data ecosystem value chain as a data intermediary. The primary objective of the Data Governance Act, which is still under negotiation, is to ensure that data trading is facilitated by analytics-neutral data intermediaries. The reData.me platform fully complies with this requirement.

